The Leopard 2 is a main battle tank (main battle tank MBT), developed by the German Krauss-Maffei in the early 1970s and began to be used in 1979. Leopard 2 replace Leopard 1 as the main battle tank of the German Army.
Leopard 2 adalah tank tempur utama (main battle tank, MBT) Jerman yang dikembangkan oleh Krauss-Maffei pada awal 1970-an dan mulai digunakan pada 1979. Leopard 2 menggantikan Leopard 1 sebagai tank tempur utama Angkatan Darat Jerman.
German-made Leopard 1 tanks were first used in 1956. Tank is also a main battle tank (main battle tank) in several countries in the world. Leopard 1 as the main battle tank of the German Army. Leopard 2 tanks developed since 1970 and first launched in 1979 to replace. Leopard is also used in twelve other European countries, and those countries with a non-European. The Leopard 2 is, undoubtedly, is one of the most successful tanks of the last generation MBT, and more than 3,200 units have been produced.
Tank Leopard 1 buatan Jerman pertama kali digunakan pada tahun 1956. Tank ini juga menjadi tank tempur utama (main battle tank) di beberapa negara di dunia. Leopard 1 sebagai tank tempur utama Angkatan Darat Jerman. Tank Leopard 2 dikembangkan sejak tahun 1970 dan diluncurkan pertama pada tahun 1979 untuk menggantikan. Leopard juga digunakan di dua belas negara Eropa lainnya, serta negara-negara non-Eropa. Leopard 2, tak diragukan lagi, adalah salah satu tank tersukses dari generasi terakhir MBT, dan lebih dari 3.200 unit telah diproduksi.
Indonesia, the country with the largest economy in Southeast Asia, it has previously indicated it would buy 130 Leopard tanks from Rheinmettal AG as part of the military defense equipment modernization program worth 15 billion dollars for five years (2010-2014) Merkel during a visit to Indonesia in 2012. Initial estimate of the value at the time was 280 million dollars to 130 tanks.
Indonesia, negara dengan ekonomi terbesar di Asia Tenggara, sebelumnya memang telah mengindikasikan akan membeli 130 tank Leopard dari Rheinmettal AG sebagai bagian dari program modernisasi alutsista TNI senilai 15 miliar dolar untuk lima tahun (2010-2014) saat kunjungan Merkel ke Indonesia pada 2012 lalu. Nilai perkiraan awal pada saat itu adalah 280 juta dolar untuk 130 tank.
"Leopard is already modified and it will be used for the tropics. Hence the name Leopard adjusted RI because it can be used in tropical areas, "he said on Tuesday (21/5). Leopard tanks from Germany will come. The tank has been modified and will be labeled 'Leopard RI'. Leopard tanks name'''' reminiscent of The Javan Leopard , leopard ie, specific species that exist in Java. In 2008, this species is classified endangered.
“Leopard itu sudah dimodifikasi dan itu akan terpakai untuk daerah tropis. Karena itu namanya Leopard RI karena sudah di adjusted yang bisa dipakai didaerah tropis,” katanya, Selasa (21/5). Tank Leopard dari Jerman akan datang. Tank tersebut sudah dimodifikasi dan nantinya akan berlabel ‘Leopard RI’. Nama tank ''Leopard'' mengingatkan pada The Javan Leopard, yakni macan tutul, spesies khusus yang ada di Pulau Jawa. Pada tahun 2008, spesies ini masuk klasifikasi terancam punah.
At first, the government would only get 44 Leopard Tank. However, he felt quite lucky because the budget 44 new tanks, Indonesia would be able to get around 160 Leopard Tank. "At first, with the same money, we can only count 44 brand new (tank). But with the same money we could get 100 battle tanks play continues we may again about 50 medium battle tank, "he said.
Tadinya, pemerintah hanya akan mendapatkan 44 Tank Leopard. Tetapi, ia merasa cukup beruntung karena dengan anggaran 44 tank baru, Indonesia justru bisa mendapatkan sekitar 160 Tank Leopard. “Tadinya, dengan uang yang sama, kita hitung hanya dapat 44 brand new (tank). Tapi dengan uang yang sama kita bisa mendapatkan 100 main battle tank terus kita dapat lagi sekitar 50 medium battle tank,” katanya.
Package purchase Leopard Tank Indonesia reached 163, consisting of 63 Leopard 2 MBT Revolusion, 40 Leopard 2A4, Unit 10 supporters and 50 Medium Tank Tank Marder 1A3. The amount represents the amount of obstruction is quite fantastic and will make the Indonesian army forces will increase drastically. Indeed, of the 163 is only 103 Tank Leopard 2 MBT, the rest are 10 Tank supporter. The remaining 50 Marder 1A3, is not included in the category of MBT, but it is a Medium Tank.
Paket pembelian Leopard Indonesia mencapai 163 Tank, yang terdiri dari 63 MBT Leopard 2 Revolusion, 40 leopard 2A4, 10 Unit Tank pendukung dan 50 Medium Tank Marder 1A3. Jumlah tersebut merupakan sebah jumlah yang cukup fantastis dan akan membuat kekuatan angkatan darat Indonesia akan meningkat secara drastis. Memang dari 163 Tank tersebut hanya ada 103 MBT Leopard 2, selebihnya adalah 10 Tank pendukung. Sisanya 50 Marder 1A3, bukan termasuk dalam kategori MBT, tetapi merupakan Medium Tank.
INDONESIA BUY 40 UNITS OF THIS TANK. families Leopard 2A4 MBT Leopard is the most digunakaan today. Leopard 2A4 is a development of the Leopard 2A3, where a lot of substantial changes in this series. An example is the automated fire and explosion suppression system that is all-digital could fire a variety of ammunition types most accurately and is also equipped with armor perlingungan much better than previous models.
INDONESIA MEMBELI 40 UNIT TANK JENIS INI. Leopard 2A4 adalah keluarga MBT Leopard yang paling banyak digunakaan saat ini. Leopard 2A4 ini merupakan pengembangan dari Leopard 2A3, dimana banyak sekali perubahan substansial dalam seri ini. Contohnya adalah automated fire and explosion suppression system yang sudah serba digital yang bisa menembakkan berbagai type amunisi terbaru secara akurat dan juga dilengkapi dengan armor perlingungan yang jauh lebih baik dari model sebelumnya.
The Leopard 2 is built in 8 batches between 1985 and 1992. And all previous versions are also upgraded to 2A4 standard. Until the year 1994, operates about 2,125 German MBT Leopard 2A4 (2A4 695 is new, the rest is an upgraded version of the old). Leopard 2A4 also in production license to the Swiss who finally called the Pz 87. Switzerland currently operates approximately 380 MBT PZ 87.
Leopard 2 ini di bangun dalam 8 batch antara tahun 1985 sampai 1992. Dan semua versi sebelumnya juga diupgrade menjadi standard 2A4. Sampai dengan tahun 1994, Jerman mengoperasikan sekitar 2.125 MBT Leopard 2A4 (695 adalah 2A4 baru, sisanya merupakan upgrade versi lama). Leopard 2A4 juga di produksi secara lisensi kepada Swiss yang akhirnya disebut dengan Pz 87. Saat ini Swiss mengoperasikan sekitar 380 MBT PZ 87.
After the end of the cold war era, Germany sense that they no longer need the MBT in large numbers. To that end, Germany ended up selling most of the Leopard 2A4 MBT them to other countries. MBT over Germany was eventually bought by Austria (114), Canada (107), Chile (140), Denmark (51), Finland (139), Greece (183), Norway (52), Poland (128), Portugal ( 37), Singapore (96), Spain (108), Sweden (160) and Turkey (339). If Indonesia really bought this leopard tank MBT, Indonesia is a country that buys surplus umpteenth German MBT's. Following on the back of Indonesia possibility is the Philippines are interested in buying about 30 Leopard 2A4 MBT German surplus.
Setelah berakhirnya era perang dingin, Jerman merasakan bahwa mereka tidak lagi memerlukan MBT dalam jumlah yang banyak. Untuk itu, Jerman akhirnya menjual sebagian besar MBT Leopard 2A4 mereka ke negara lain. MBT lebih dari Jerman tersebut akhirnya dibeli oleh Austria (114), Kanada (107), Chile (140), Denmark (51), Finlandia (139), Yunani (183), Norwegia (52), Polandia (128), Portugal (37), Singapura (96), Spanyol (108), Swedia (160) dan Turki (339). Jika Indonesia benar-benar membeli tank MBT leopard ini, maka Indonesia adalah negara kesekian yang membeli surplus MBT Jerman ini. Menyusul di belakan Indonesia kemungkinan adalah Filipina yang juga tertarik membeli sekitar 30 MBT Leopard 2A4 surplus Jerman.
It was clear that 40 Leopard 2A4 MBT MBT is not a new, but used German military. However, that does not mean junk Used MBT, MBT is true is because one of the best MBT in the world. Germany sold not because MBT is not good anymore, but because Germany has a surplus of MBT are very much the rest of the cold war era ago. Now they have to sell it to reduce maintenance costs as well as get fresh money from sales to other countries.
Jelas sekali bahwa 40 MBT Leopard 2A4 ini bukan merupakan MBT baru, namun bekas pakai militer Jerman. Namun, MBT Bekas bukan berarti rongsokan, karena MBT ini sejatinya adalah salah satu MBT terbaik di dunia. Jerman menjualnya bukan karena MBT ini sudah tidak bagus lagi, namun karena Jerman memiliki surplus MBT yang sangat banyak sisa dari era Perang dingin dahulu. Sekarang mereka harus menjualnya untuk mengurangi biaya maintenance serta mendapatkan uang segar dari penjualannya ke negera lain.
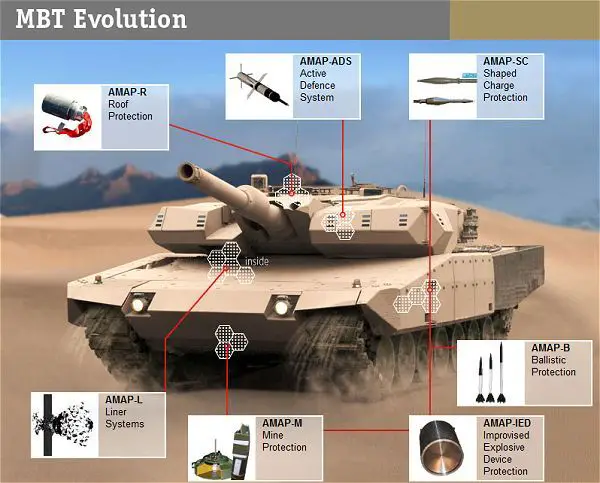
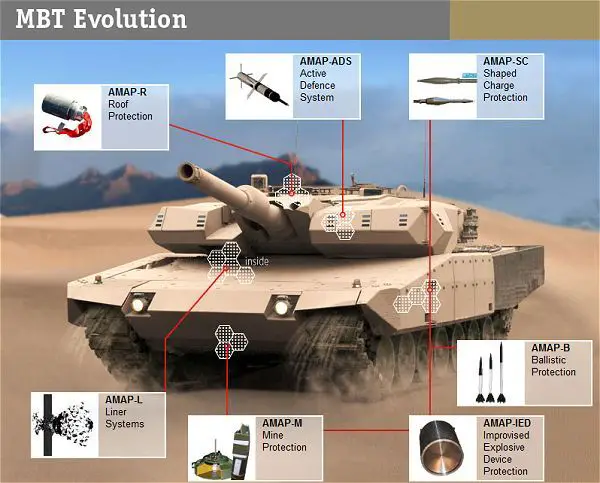
INDONESIA BUY 63 UNITS OF THIS TANK. Leopard 2 Revolution is the Leopard 2A4 upgraded in many ways. Leopard 2 Revolution is better than Leopard 2A4 dalamurban warfare. MBT has improved the performance of this type of protection that comes with the new composite armor package Advanced Modular Armor Protection (AMAP). This new armor provides a level of protection far higher than the enemy's attack. Leopard 2 Revolution is equipped with modular armor, which means that the damage to the armor modules can be overcome by replacing the damaged armor alone. In addition to the MBT is fitted with a grenade launcher as a form of self defense.
INDONESIA MEMBELI 63 UNIT TANK JENIS INI. Leopard 2 Revolution ini adalah Leopard 2A4 yang di upgrade dalam banyak hal. Leopard 2 Revolution ini lebih baik dari Leopard 2A4 dalamurban warfare. MBT jenis ini sudah ditingkatkan performa proteksinya yang dilengkapi dengan paket armor komposit baru yaitu Advanced Modular Armor Protection (AMAP). Armor baru ini memberikan tingkat perlindungan yang jauh lebih tinggi dari serangan musuh. Leopard 2 Revolution ini dilengkapi dengan modular armor, yang berarti bahwa kerusakan pada satu modul armor dapat diatasi dengan mengganti armor yang rusak itu saja. Selain itu MBT ini dilengkapi dengan pelontar granat sebagai bentuk pertahanan diri.


If Indonesia really buy Leopard 2 Revolution this, Indonesia will be the second country in ASEAN that operate this type of leopard. Previously Singapore also already operates 96 Leopard 2A4 were upgraded to leopard 2 Revolution, which eventually called the Leopard 2SG. Compared with the Leopard 2A4 standard that weighs 56.6 tons, the Leopard 2 Revolution has a weight of about 60 tons.
Jika Indonesia benar-benar membeli Leopard 2 Revolution ini, maka Indonesia akan menjadi negara kedua di ASEAN yang mengoperasikan leopard jenis ini. Sebelumnya Singapura juga sudah mengoperasikan 96 Leopard 2A4 yang di upgrade menjadi leopard 2 Revolution, yang akhirnya disebut dengan Leopard 2SG. Dibandingkan dengan Leopard 2A4 standard yang memiliki bobot 56.6 Ton, maka Leopard 2 Revolution ini memiliki bobot sekitar 60 ton.
- Tank Pendukung Leopard 2 AVLB (Armored Vehicle Launched Bridge)
INDONESIA BUY 10 UNITS OF THIS TANK. Perhaps many people who still do not understand why there should be a Tank Leopard 2 tanks supporting this. As we know that MBT is a very heavy vehicle, thus requiring support to be able to move freely in various battlefield. An example is the battlefield that is passed in the form of rivers where there is only a small bridge that does not allow to pass Leopard weighing up to 60 tons. Or if there are events Leopard tanks mired into a hole or something that must be raised by another vehicle. Sure to lift the tank weighing 60 tons in need of a machine that has the extra power to it. Here was this support perluanya tank.
INDONESIA MEMBELI 10 UNIT TANK JENIS INI. Mungkin banyak pihak yang masih belum memahami kenapa harus ada tank pendukung Tank Leopard 2 ini. Seperti kita ketahui bersama bahwa MBT adalah kendaraan yang sangat berat, sehingga membutuhkan support agar bisa bergerak leluasa di berbagai medan tempur. Sebagai contoh adalah medan tempur yang dilalui adalah berupa sungai-sungai dimana hanya terdapat jembatan kecil yang tidak memungkinkan untuk dilalui Leopard yang beratnya mencapai 60 Ton. Atau jika ada kejadian tank Leopard ini terperosok kedalam lubang atau apalah sehingga harus diangkat oleh kendaraan lain. Tentu untuk mengangkat Tank seberat 60 ton di perlukan mesin yang memiliki tenaga extra untuk itu. Disini lah perluanya tank pendukung ini.
To overcome the limitations of the bridge has been developed variant for Leopard Leopard version avlb (Armored Vehicle Launched Bridge) which serves to provide a portable bridge with a length of about 15-30 meters. This variant Leopard 2 is a true leopard 2 which Hull for his gun replaced with a portable bridge. With the existence of this variant as a supporting tank leopard, the criticism has been that Leopard will not be beropareasi in Indonesian bridge is wrong. Because it can be overcome with the Leopard tanks supporting this.
Untuk mengatasi keterbatasan jembatan untuk Leopard telah dikembangkan varian Leopard versi AVLB (Armored Vehicle Launched Bridge) yang berfungsi untuk menyediakan jembatan portable dengan panjang sekitar 15-30 meter. Varian Leopard 2 ini sejatinya adalah leopard 2 yang mana Hull untuk senjatanya diganti dengan jembatan portable. Dengan adanya varian ini sebagai tank pendukung leopard, maka kritikan selama ini bahwa Leopard tidak akan bisa beropareasi di jembatan Indonesia adalah salah. Karena itu bisa diatasi dengan adanya tank pendukung Leopard ini.
Look at the picture below, which is a bridge that carried out the installation process by supporting Leopard 2 tanks.
Perhatikan gambar di bawah ini, yang merupakan proses pemasangan jembatan yang dilakukan oleh tank pendukung Leopard 2.
While to deal with the heavy lifting, can be done with 2 leopard variant called the Buffel. Buffel 2 leopard variant is indeed devoted to handle cases like this.
Sedangkan untuk menangani masalah angkat berat, dapat dilakukan dengan varian leopard 2 yang disebut dengan Buffel. Buffel ini memang varian leopard 2 yang dikhususkan menangani kasus seperti ini.




INDONESIA BUY 50 UNITS OF THIS TANK. then that makes the purchase of German Leopard 2 is more impressive is the inclusion of 50 units as part of the package Marder 1A3 leopard to Indonesia. As we know that Indonesia has long wanted to build a Medium Tank ToT own. And it seems the German ToT will be given to Indonesia is ToT to build based Marder 1A3 Medium Tank was purchased. If this is indeed the case then this ToT will provide enormous strategic impact for Indonesia in the future.
INDONESIA MEMBELI 50 UNIT TANK JENIS INI. Selanjutnya yang membuat pembelian Leopard 2 dari Jerman ini semakin berkesan adalah disertakannya 50 unit Marder 1A3 sebagai bagian paket leopard ke Indonesia. Seperti kita ketahui bahwa Indonesia sudah sejak lama menginginkan ToT untuk membangun Medium Tank sendiri. Dan agaknya ToT yang akan diberikan Jerman ke Indonesia adalah ToT untuk membangun Medium Tank berbasis Marder 1A3 yang dibeli ini. Jika hal ini memang benar terjadi maka ini ToT ini akan memberikan dampak strategis yang sangat besar bagi Indonesia di masa yang akan datang.


ToT medium tank will greatly help PINDAD that had seemed very keen to develop its own Medium Tank. ToT Marder 1A3 is a kesematan gold for Indonesia foot toward independence gate defense equipment in the future.
ToT medium tank ini akan sangat membantu Pindad yang selama ini sepertinya sangat getol ingin mengembangkan Medium Tank sendiri. ToT Marder 1A3 ini adalah sebuah kesematan emas untuk melangkahkan kaki Indonesia menuju gerbang kemandirian alutsista di masa yang akan datang.
Leopard 2 tanks will be placed in 8/Tank Cavalry Battalion Unit with panther emblem will be fierce when reinforced with tanks'' Leopard''. Cavalry Battalion (Yonkav) 8 located in Beji, Pasuruan. During this time, a stronghold of defense equipment Yonkav 8 Scorpion and Stormer armored vehicles.
Tank Leopard 2 ini akan ditempatkan di Satuan Batalyon Kavaleri 8/Tank dengan lambangnya macan kumbang akan semakin garang saat diperkuat dengan tank ''Leopard''. Batalyon Kavaleri (Yonkav) 8 berkedudukan di Beji, Pasuruan. Selama ini, Yonkav 8 menjadi markas alutsista kendaraan tempur Scorpion dan Stormer.
Author : Yohanes Gitoyo.
Source :
- http://id.wikipedia.org/wiki/Leopard_2
- http://militerindonesiamy.blogspot.com/2012/09/analisis-indonesian-mbt-63-leopard-2.html
- http://afrid-fransisco.blogspot.com/2013/02/leopard-revolution-tank-canggih.html
- http://www.republika.co.id/berita/nasional/umum/13/05/21/mn5eaj-alutsista-dari-jerman-berlabel-leopard-ri
- http://www.artileri.org/2013/05/jerman-jual-164-tank-ke-indonesia.html