Superman, is a fictional superhero character's most famous and influential of comics publisher DC Comics from the United States. Superman has been widely regarded as a cultural icon who symbolizes the power of the United States culture.
In English, Superman also known as "The Man of Steel" ("Man of Steel") "The Man of Tomorrow" ("Man of the Future") and "The Last Son of Krypton" ("Last Son of Krypton Planet"). Superman was given the nickname by his colleagues superhero friend with the nickname "The Big Blue Boy Scout" ("Son of Big Blue Boy Scout a man").
Invented by a Canadian artist, Joe Shuster and American writer Jerry Siegel in 1932 when they were teenagers in Cleveland, Ohio and then sell it to Detective Comics, Inc.. in 1938. Superman first appeared in Action Comics series ("Action Comics") issue # 1 in the United States (June 30, 1938) and later also appeared on numerous radio drama series, television shows, feature films, newspapers, comics, novels, and English video game. With the success of his adventures, Superman helped create the variety and popularity of super hero comic books United States.
History.
"The Reign of the Super-Man" in Science Fiction, Vol. 1, No. 3 (June 1933).
When Jerry Siegel and Joe Shuster first created Superman, not a super hero who is always helping other people, but a bald genius psychopath with telepathic powers who want to rule the whole world. He appeared in a short story entitled "The Reign of the Super-Man" from Science Fiction # 3, a magazine published by Siegel in 1933. Because his behavior is not this character, in the end "Balding Superman" that was subsequently rewritten by Siegel in the year 1933 as a hero, is different from previous bad character, was modeled on actor Douglas Fairbanks Sr. and his alter ego Clark Kent, on Harold Lloyd comedy actor. Superman evil bald and then became an archenemy of Superman named Lex Luthor.
As told in the Action Comics issue # 1, Superman was born on the planet Krypton as Kal-El, and when an infant was launched by rocket to Earth by his father, Jor-El, moments before the planet was destroyed. Rockets later landed on Earth, in a field, which was discovered by a couple Kent, Jonathan Kent and Martha Kent, who later adopted him and named Clark Kent. As a child growing up, he found that he had mastered the power that is far above ordinary people and uses his powers to help others. To hide his identity secret when you're not dealing with criminals as a Superman, he lived as Clark Kent, mild-mannered human being, a reporter for The Daily Star (later renamed The Daily Planet). Clark worked with reporter Lois Lane, and involved a romance with him, and told married in advanced comic story.
Logo S
Superman was the first super hero character who wears eblem or a logo on the chest. The design of the original characters do not wear any emblems, but because of the times and the time, then added the mark "S" is. For the creators "S" can also be derived from the acronym "Shield" (shield). Her Logo is the original form of the Badges Police cheat in America, but after Superman became famous, the logo was better known as "The Knight Shield".
Personality Characteristics
In early pernciptaan by Siegel and Shuster, Superman has a rugged and aggressive personality. The characters you see in the steps to stop domestic violence, the moneylenders, gangsters and mobsters, with slightly rough and lack the moral code for the viewer can be used at this time. Then there are writers who have softened the character and instilled a sense of idealism and moral code of conduct. Although not sesadis / cold character in the early days of Batman, Superman appeared in comics in the 1930s cares not told about the dangers that can be caused by strength, throw the criminals in a way that will cause death if only occur, although this is not shown explicitly uncommon on the page. This story came to an end late 1940, when a new editor is named Whitney Ellsworth provide code for this character, banning Superman to ever kill someone.

Clark Kent, Superman's secret identity, was based partly on Harold Lloyd and named after Clark Gable and Kent Taylor. Creators have discussed the idea of whether Superman pretends to be Clark Kent or vice versa, and sometimes different in publications both approaches have been adopted.
Although typically a newspaper reporter, during the 1970s the character left the Daily Planet for a time to work for television, whilst the 1980s revamp by John Byrne saw the character become somewhat more aggressive. This aggressiveness since faded with subsequent creators restoring the traditional gentle nature to the character.
Personal Data
- Surname: Clark Kent (Planet Earth) / Kal-El (Planet Krypton)
- Status: Married
- Height: 6'3 "(192 024 cm)
- Weight: 102.1 kg
- Eye Color: Blue
- Hair: Black
- Alias: Man of Steel, Man Of Tomorrow, Last son of Krypton and Krypton's favorite son
- Occupation: Adventurer, a newspaper reporter, columnist, novelist, former editor,
- Group Affiliation: Justice League of America (currently); Justice League International
- Address: Metropolis, USA
Family
- Jor-El (birth father; deceased);
- Lara (biological mother; deceased);
- Jonathan Kent (adoptive father),
- Martha Clark Kent (foster mother);
- Lois Lane (wife);
- Harry Kent (adoptive uncle);
- Sarah Kent (adoptive aunt);
- Jason White (biological children);
Age and birthday Superman.
Age Superman has varied through history in comics. He's initially defined, with real-time references to specific years are sometimes given to past events in the beginning of the Golden Age and Silver Age comics. In the comics published between the 1970s and early 1990s, he was usually quoted as 29 years. However, during the Death of Superman storyline, Clark age was given as 34 years (in the paper published fiction promotion), while the Zero Hour time in 1994 founded his age as 35.
In the Golden Age, 1950 Action Comics # 149 gives birth date of October as Superman. In the Silver Age and Bronze Age stories, Superman's birthday on February 29 is described as a, as shown in Superman Annual # 11 in 1985. Clark Kent, meanwhile, will celebrate his birthday on June 18, the date was first discovered Clark Kents (June 18, also born of Superman voice actor Bud Collyer.) Post-Crisis story also references a February 29 re Clark Kent, as shown in Action Comics # 655 (July 1990). However, in 2009 Superman: Secret Origin describe Clark celebrated his birthday on December 1st.
Superman biography.
Details of Superman's origin, relationships and abilities changed significantly during the publication of the character, from what is considered the Golden Age of Comic Books through the Modern Age. Powers and villains were developed through the 1940s, with Superman developing the ability to fly, and costumed villains introduced from 1941. The character has learned the existence of Krypton is shown in 1949. The concept itself was originally founded in 1939 for the readers in the Superman comics.
The 1960s saw the introduction of a second Superman. DC has created a multiverse within the fictional universe of the character. This allows the characters published in the 1940s to exist alongside colleagues published updated in 1960. It is explained to the reader through the notion that the two groups of characters inhabited parallel Earth. The second Superman was introduced to explain to the reader Superman's members in both the 1940s superhero team the Justice Society and the American 1960s superhero team the Justice League of America.
The 1980s saw a radical revision of the character. DC decided to remove the multiverse in a bid to simplify its comics line. This led to the rewriting of the back story of the characters DC published, Superman included. John Byrne rewrote Superman, move back a lot of terms defined and the characters from continuity, including Superboy and Supergirl. Byrne also re-established Superman's adoptive parents, The Kents, as characters. In a previous story, the character has been written as had died in early life of Superman (Clark Kent on the time of graduation from high school).
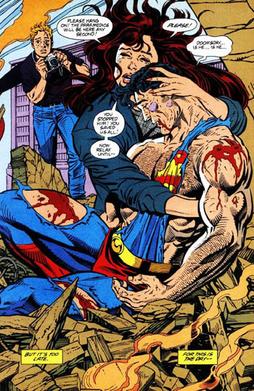
Superman Lois Lane dies at arm 's: Superman No. 75 (vol. 2 January 1993), Art by Dan Jurgens and Brett Breeding
In 1992 Superman was killed by the villain Doomsday, although the character immediately resurrected the following year. Superman married Lois Lane in 1996. His origins back in 2004. In 2006 Superman stripped of their power, although this is returned within one year of fiction.
Superman vs. Doomsday battle video on Youtube,
Click the link to watch.
Superman: Doomsday - The Death of Superman Part 1
Superman: Doomsday - The Death of Superman Part 2
Superman: Doomsday - The Death of Superman Part 3
Superman: Doomsday - The Death of Superman Part 4
Superman: Doomsday - The Death of Superman Part 5
After a confrontation with Brainiac that resulted in the deaths of his father, Superman found the lost city of Kandor, which contains 10,000 Kryptonians. They stay on Earth causes trouble, and the Kryptonians create their own planet, New Krypton. Eventually, New Krypton wages war against Earth. Both sides retain large casualties and most of the Kryptonians killed. Superman then begins journey to reconnect with his adopted home world.
Strengths and capabilities.
As an influential archetype of the superhero genre, Superman has extraordinary powers, with the character traditionally described as "faster than a speeding bullet, more powerful than a locomotive, and able to leap tall buildings in a single bound", a phrase coined by Jay Morton and first first used in the Superman radio serials and Max Fleischer animated shorts in the 1940s, as well as TV series in the 1950s.
For most of his existence, Superman's famous arsenal:
- aviator super
- super strength
- immunity to non-magical attacks, super-speed,
- power of vision (including x-ray, heat-emitting, telescopic, infra-red, and microscopic vision)
- super hearing
- ability to think super
- super breath, which enables him to blow out air at freezing temperatures, as well as exerting a driving force of high-speed winds.

As originally conceived and presented in the beginning of the story, Superman's strength is relatively limited, consisting of superhuman strength that allowed him to lift a car over his head, run at amazing speeds and leap one-eighth of a mile, and very dense body structure that could not be penetrated by less than an artillery shell exploded. Siegel and Shuster compared the strength and jumping abilities of ants and grasshoppers. When making the cartoons, the Fleischer Brothers found it difficult to keep him jump and turn requested to DC to change his ability to fly,. This is a very convenient concept for short films, which would otherwise have wasted valuable time running earthbound Clark Kent moves from place to place.
Writers gradually increased his powers to larger extents during the Silver Age, in which Superman could fly to other galaxies and the world and even in the entire universe with relative ease. He often fly across the solar system to stop meteors from hitting the Earth, or sometimes just to clear his head.
Writers found it increasingly difficult to write Superman stories in which the character was believably challenged, so DC made a series of attempts to rein the character entered the most significant attempt, John Byrne's 1986 rewrite, established several hard limits on his ability: he barely survives a nuclear blast, and his space flights are limited by how long he can hold his breath. Superman's power levels have again increased since then, with Superman currently has enough strength to hurl mountains, withstand nuclear blasts with ease, fly into the sun unharmed, and survive in the vacuum of outer space without oxygen.
Source of strength Superman has subtly changed during its history. It was originally stated that Superman's abilities derived from Kryptonian heritage, which made him eons more evolved than humans, this soon changed, with the source of power is now based upon the establishment of Krypton gravity as having been stronger than the Earth. This situation reflects that Edgar Rice Burroughs' John Carter. As Superman strength increased, the implication that all Kryptonians have the same ability to be a problem for the author, so it is doubtful that a race of such beings could have been destroyed by something as trivial as the planet explodes. In part to counter this, Superman writers established that Kryptonians, whose native star Rao had been red, have a super power only under the light of a yellow sun.
Superman is most vulnerable to green Kryptonite, mineral debris from Krypton transformed into radioactive material by the forces that destroyed the planet. Exposure to green Kryptonite Superman cancel strength and immobilize him with pain and nausea, prolonged exposure will eventually kill him.
The only substance on Earth that can protect him from Kryptonite is lead, which blocks the radiation. Lead is also the only known substance that Superman can not see through with his x-ray vision. Kryptonite was first introduced to the public in 1943 as a plot device to allow the radio serial voice actor, Bud Collyer, to take some time. Although green Kryptonite is the most commonly seen form, writers have introduced other forms over the years: such as red, gold, blue, white, and black, each with its own effect.
Superman enemy.
Superman also has enemies, including the most well-known nemesis, Lex Luthor, who has been envisioned over the years in various forms either as a genius scientist who jerk with personal grudges against Superman, and powerful but corrupt CEO of a conglomerate called LexCorp who thinks Superman is somehow inhibited human progress by his heroic efforts.
In the 2000s, he even became president of the United States, and has been described generally as a former childhood friend of Clark Kent. The alien android (in most incarnations) known as Brainiac is considered by Richard George to be the second most effective enemy of Superman.
Enemies who achieved the most, by actually killing Superman, is the raging monster Doomsday. Darkseid, one of the most powerful beings in the DC Universe, is also a formidable enemy in most post-Crisis comics. Other important enemies who have featured in various incarnations of the character, from comic books to film and television include the fifth-dimensional imp Mr. Mxyzptlk, the reverse Superman known as Bizarro and the Kryptonian criminal General Zod, among many others.
Superman publications.
- Serial publications Superman in Superman comics
Superman comic with his own role is not as successful at the beginning of its emergence. Superman and the JLA joined the group as its leader and become a separate comic. Superman on the other hand do the Cross-Over the hero of the other DC like Superman vs. Batman and others.
Superman's first appearance in Action Comics # 1, published on April 18, 1938 (cover-dated to June 1938). In 1939, a self-titled series was launched. The first issue mainly reprinted adventures published in Action Comics, but despite this the book achieved sales greater. 1939 also saw the publication of New York World's Fair Comics, which in the summer of 1942 became World's Best Comics. With issue No.7 of All Star Comics, Superman made the first of a number of infrequent appearances, on this occasion appearing in cameo to establish his honorary membership in the Justice Society of America.
Initially Jerry Siegel and Joe Shuster provided the story and art for all the strips published. However, Shuster eyesight began to deteriorate, and the increasing appearance of the character meant an increase in workload. This led Shuster to establish a studio to assist in the production of art, although he insisted on drawing the face of every Superman the studio produced. Outside the studio, Jack Burnley began supplying covers and stories in 1940, and in 1941 artist Fred Ray began contributing stream of Superman covers, some of which, such as that of Superman # 14 (February 1942), became iconic and much reproduced. Wayne Boring, initially working in the Shuster studio, began working for DC in his own right in 1942 providing pages for both Superman and Action Comics. Al Plastino was hired initially to copy Wayne Boring but was eventually allowed to create his own style and became one of the most prolific Superman artists during the Gold and Silver Ages of comics.
Scripting duties also became shared. In late 1939 a new editorial team in control of adventure character. Whitney Ellsworth, Mort Weisinger and Jack Schiff were taken after Vin Sullivan's departure. New editorial team brought in Edmond Hamilton, Manly Wade Wellman, and Alfred Bester, established writers of science fiction.
In 1943, Jerry Siegel was drafted into the army in a special celebration, and as a result the contribution is reduced. Don Cameron and Alvin Schwartz joined the writing team, Schwartz worked with Wayne Boring to work on the Superman comic, which had been launched by Siegel and Shuster in 1939.
In 1945, Superboy made his debut in More Fun Comics # 101. The character moved to Adventure Comics in 1946, and his own title, Superboy, was launched in 1949. 1950 saw the launch of Superman's Pal Jimmy Olsen (1954) and Superman's Girl Friend, Lois Lane (1958). In 1974 the title had merged into Superman Family, although the series was canceled in 1982. DC Comics Presents was a series published 1978-1986 featuring team-ups between Superman and other characters from the DC Universe.
In 1986, the decision was taken to restructure the universe the Superman character inhabited with other DC characters in the mini-series Crisis, resulting in the publication of "Whatever Happened to the Man of Tomorrow", a two-part story written by Alan Moore, with art by Curt Swan , George Pérez and Kurt Schaffenberger. This story was published in Superman # 423 and Action Comics # 583 and presented what Les Daniels notes as "the sense of loss the fans might have experienced if this really has been the last Superman tale."
Originally revamped Superman in The Man of Steel # 1 (July 1986), written and drawn by John Byrne.
Superman was relaunched by writer & artist John Byrne, initially in the limited series The Man of Steel (1986). 1986 also saw the cancellation World's Best Comics, and the Superman title renamed The Adventures of Superman.
A second volume of Superman was launched in 1987, running until cancellation in 2006. After this cancellation, The Adventures of Superman back to the Superman title. Superman: The Man of Steel was launched in 1991, running until 2003, while the quarterly book Superman: The Man of Tomorrow ran from 1995 to 1999.
In 2003 Superman / Batman was launched, ending in 2011 and Superman: Birthright limited series, with All-Star Superman launched in 2005 and Superman Confidential in 2006 (this title was canceled in 2008). He also appeared in the TV animated series-based comic book tie-ins Superman Adventures (1996-2002), Justice League Adventures, Justice League Unlimited (canceled in 2008) and The Legion of Super-Heroes in the 31st Century (canceled in 2008).
In 2011, DC Comics relaunched Superman comics, along with the rest of their degree. Superman and Action Comics canceled and restarted with the all-new # 1 issues. Superman's costume was redesigned to look more like armor and red shorts over tights have been removed.
Superman and Wonder Woman in Justice League shared a kiss vol. 2, # 12 (August 2013), which has since been developed into a romantic relationship.
As of 2013, the ongoing publication featuring Superman on a regular basis are Superman, Action Comics and Justice League. The character often appears as a guest star in other series and is usually a pivotal figure in DC crossover events.
- Publication Superman in the film world.
- 1948: Superman, a series in the 15 series, starring Kirk Alyn and Noel Neill.
- 1950: Atom Man Vs. Superman serial in 15 parts starring Kirk Alyn, Noel Neill and Lyle Talbot. Bertampur with Atom Man and Lex Luthor.
- 1951: Superman and the Mole Men, widescreen movie, starring George Reeves and Phyllis Coates.
- 1954: Stamp Day for Superman, short duration movie featuring George Reeves and Noel Neill promote Stamp Day for the U.S. Treasury Department.
- 1978: Superman, direction by Richard Donner and starring Christopher Reeve, Marlon Brando, Gene Hackman and Margot Kidder.
- 1981: Superman II, the direction of Richard Lester and starring Christopher Reeve, Margot Kidder, and Terence Stamp.
- 1983: Superman III, direction of Richard Lester and starring Christopher Reeve, Richard Pryor, Annette O'Toole and Robert Vaughn.
- 1984: Supergirl, film for extra income based on extra character comic, landing Jeannot Szwarc and starring Helen Slater and Faye Dunaway.
- 1987: Superman IV: The Quest For Peace, landing Sidney J. Furie and starring Christopher Reeve, Gene Hackman, Margot Kidder, and Mariel Hemingway.
- 2006: Superman Returns, Bryan Singer's direction and starring Brandon Routh, Kate Bosworth and Kevin Spacey.
- 2006: Superman II: The Richard Donner's Cut. Edits new version of Superman II movie, featuring approximately 70% additional new long taken by director Richard Donner, including new material featuring Marlon Brando.
- 2013: Man of Steel, the film directed by Zack Snyder, starring Kevin Costner, Amy Adams, Russell Crowe and Henry Cavill.
- Publication in the Superman TV Series
- 1952 - 1958: Adventures of Superman, starring George Reeves, Phyllis Coates (season 1) and Noel Neill (seasons 2-6).
- 1957: I Love Lucy - episode "Lucy and Superman" featuring George Reeves as Superman.
- 1961: The Adventures of Superboy was not aired on television series, starring Johnny Rockwell.
- 1975: It's A Bird, It's A Plane, It's Superman, for the television production of the broadway musical starring David Wilson and Lesley Ann Warren.
- 1988 - 1992: Superboy, a television series starring John Haymes Newton (1988-1989), Gerard Christopher (1989-1992) and Stacy Haiduk
- 1993 - 1997: Lois & Clark: The New Adventures of Superman, starring Dean Cain and Teri Hatcher.
- 2001 - (current): Smallville, starring Tom Welling, Michael Rosenbaum, Kristin Kreuk and Erica Durance.
- Superman publications in the Video Game.
While Superman is largely considered as the archetypal superhero, and the flagship character of DC Comics, he has enjoyed virtually no success in video games. Various Superman video game has been released, starting with Superman for the Atari 2600 in 1978, nothing has been commercially successful.
One of the most famous examples is the 1999 game for the Nintendo 64, simply titled Superman (although often erroneously called Superman 64 because of the tradition of N64 games putting the number "64" at the end of several titles), which is largely considered to be one of the worst games of all time.
"Marvel Versus DC"
In 2007, a site preselect the strongest super hero with a power that was given the title of "The Most Strength Superhero" (Indonesian: "Strongest Super Heroes"). Here is the third to occupy the position of unity.
- The Incredible Hulk (Marvel comic)
- Superman (from DC comic)
- The Thing from the Fantastic Four (Marvel comic)
But then, DC in collaboration with Marvel comics publishing joint entitled "DC vs. Marvel". At this comic brought together several prominent DC against Marvel characters. And among the winners of The Incredible Hulk 1 against Supeman reunited. And in this fight, Superman manages to defeat The Incredible Hulk which means undermining the notion that the Hulk is stronger than Superman. Even The Thing which occupies the third position was defeated by Martian Manhunter is back undermine the position of The Thing.
Critical reception and popularity.
Barack Obama as Superman, Los Angeles, California.
The character of Superman and various comic series have received various awards over the years.
- Magazine "Empire" named greatest comic book character of all time
- Superman government which is one of many storylines or works have received Comics Buyer's Guide for the Fan Award, winning the Favorite Comic Story category in 1993
- Superman came at number 2 in VH1's Top Pop Culture Icons 2004
- Also in 2004, "cinemagoers" English as Superman's greatest superhero of all time
- Works featuring the character have also garnered six Eisner Awards and three Harvey Awards, either to work alone or creator of the work
- Superman films have received a number of nominations and awards, with Christopher Reeve winning a BAFTA for his performance in Superman: The Movie
- The Smallville television series has garnered Emmys for crew members and various other awards.
Copyright issues.
Joe Shuster and Jerry Siegel, the BBC © BBC Four (1981)
As part of the deal which saw Superman published in Action Comics, Siegel and Shuster sold the rights to the company in exchange for $ 130 and a contract to supply the publisher with material.
The Saturday Evening Post reported in 1940 that the pair was each being paid $ 75,000 per year, a fraction of the millions of National Comics Publications' Superman profits. Siegel and Shuster renegotiated their deal, but bad blood lingered and in 1947 Siegel and Shuster sued for their 1938 contract to be made void and the re-establishment of their ownership of the intellectual property rights of Superman. The pair also sued National in the same year over the rights Superboy, which they claimed was a separate creation that National had published without authorization. National immediately fired them and took their byline on the story, prompting a legal battle that ended in 1948, when a New York court ruled that the 1938 contract should be upheld. However, the decision of Judge J. Young Addison rights granted Siegel Superboy. A month after the Superboy judgment the two sides agreed on a settlement. National paid Siegel and Shuster $ 94,000 to drop all claims. The pair also acknowledged in writing the company ownership of Superman, to prove that they hold the rights for "all other forms of reproduction and presentation, whether now existing or which may hereafter be created", but DC refused to re-employ them.
In 1973 Siegel and Shuster again launched a suit claiming ownership of Superman, this time basing the claim on the Copyright Act of 1909 which saw copyright granted for 28 years, but allowed for an additional 28-year extension. Their argument was that they had granted DC the copyright for only 28 years. The pair again lost this battle, both in a district court ruling October 18, 1973 and an appeal court ruling dated December 5, 1974.
In 1975 after news reports of the existence of the poor as they were, Warner Communications gave Siegel and Shuster lifetime pensions of $ 20,000 per year and health care benefits. Jay Emmett, then executive vice president of Warner Bros., as quoted by The New York Times stating, "There is no legal obligation, but I sure feel there is a moral obligation on our part." Heidi MacDonald, writing for Publishers Weekly, noted that in addition to this pension "Warner agreed that Siegel and Shuster would later be credited as creators of Superman on all comics, TV shows and movies".
Years after the completion of, 1976, the copyright term was extended again, this time for 19 years with a total of 75 years. However, this time a clause inserted into the extension to allow authors to reclaim their work, reflecting the arguments Siegel and Shuster had made in 1973. The new law came into force in 1978 and allows the reclamation window in the period based on the previous copyright term of 56 years. This meant the copyright on Superman could be reclaimed between 1994 to 1999 based on the initial publication date of 1938. Jerry Siegel died in January 1996, his wife and daughter filed a copyright termination notice in 1999. Although Joe Shuster died in July 1992, no termination was filed at the time by his estate.
In 1998, the copyright was extended again with the Sonny Bono Copyright Term Extension Act. This time the copyright term was extended to 95 years with a further window for reclamation introduced. In January 2004 Mark Peary, nephew and legal heir to Joe Shuster's estate, filed notice of his intent to reclaim Shuster half of the copyright, the termination effective in 2013. Siegel shares the status of copyright is now the subject of legal battles. Warner Bros. and Siegel had a discussion about how to address the issues raised by the termination notice, but these discussions aside by Siegel and in October 2004 they filed suit alleging copyright infringement on the part of Warner Bros. Warner Bros. counter sued, alleging that the termination notice contains defects , among other arguments.
On March 26, 2008, Judge Larson of the United States District Court for the Central District of California ruled that Siegel's estate was entitled to claim stake in U.S. copyright. The decision does not affect the International rights, which Time Warner hold on the character through DC. The issue of the amount of money borrowed and whether the claims Siegel real estate has extends to derivative works such as movie versions will be settled at trial, although any compensation would be owed only from works published since 1999. Time Warner does not give a statement on the ruling but has the right to challenge it. The case is scheduled to be heard in California federal court in May, 2008.
A notice of termination-of-copyright the same filed in 2002 by Siegel's wife and daughter on the Superboy character was ruled in their favor on March 23, 2006. However, on July 27, 2007, the same court issued a ruling reversing the March 23, 2006 ruling. This ruling is currently subject to a legal challenge from Time Warner, with the case unresolved.
Jerry Siegel, with wife Joanne and daughter Laura in 1976. Joanne and Laura Siegel filed a termination notice on Jerry Siegel shares Superman copyright in 1999.
A dated July 9, 2009, verdict on the case denied a claim by Siegel's family that it was owed licensing fees. U.S. District Court Judge Stephen G. Larson said Warner Bros. and DC Comics have fulfilled their obligations under the agreement for the distribution of profits Siegel for the 2006 film Superman Returns and the CW series Smallville. However, the court also ruled that if Warner Bros. does not start a new Superman movie in 2011, the family will have the right to sue to recover damages. Warner Bros. hired David S. Goyer to write the script and Christopher Nolan to produce in 2010.
On January 10, 2013, the 9th Circuit Court of Appeals ruled that the 2001 agreement that had been reached with the Siegel family of DC Comics still legally binding, thus quashing 2008 decision in favor of Siegel. The copyright only effectively ensure the DC Comics' Superman.
Author : Yohanes Gitoyo.
Reference :
- http://id.wikipedia.org/wiki/Superman
- http://en.wikipedia.org/wiki/Superman
Source : http://pustakadigitalindonesia.blogspot.com/, 4/21/2013 03:16:00 AM.